“The password you entered is incorrect. Please try again.” How many of us see this message on a regular basis and sigh in frustration at the need to reset the password yet again. Behind every user who needs to change their password on a work-related system is a frustrating system offering an unfriendly user experience and leaving companies wide open to data breaches.
In a small company with only a few employees, it may not be the biggest deal when passwords are forgotten and need to be reset every few days. But, in bigger companies with upwards of 500 employees for example, think how much time is wasted each time an employee can’t access an enterprise application and has to spend time on password resets. And, the IT team is also forced to deal with password management issues, taking time away from critical security issues.
Book a demo today to see GlobalDots is action.
Optimize cloud costs, control spend, and automate for deeper insights and efficiency.

Imagine a World With No Passwords
In a world where iris scans allow entry into a foreign country, surely there is a better and more efficient way to give employees access to enterprise networks and systems. A way that does not rely on the antiquated method of having to remember a ton of passwords, each with their own complicated set of rules. Yes, the world is more than ready for a passwordless future!
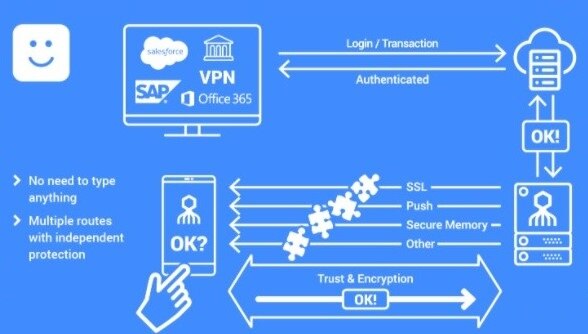
Passwordless authentication – while a mouthful to say – is the key to simplifying and streamlining the process of connecting employees to all systems company-wide, whether on-premise or in the cloud, whether online or offline. Simpler and more secure than traditional multi-factor authentication (MFA) platforms, passwordless authentication provides a seamless user experience and high assurance security. Ultimately, the company will see reduced costs because of the decrease in employee downtime (meaning increased productivity) and less expenditure on investigating and mitigating certain types of data breaches.
The Password is…Obsolete
Passwords are soon to be a thing of the past, gone in the way of CD players and landlines. Once you go passwordless, you will never look back and here are the three main reasons why:
Security
81% of successful hacking attempts are due to weak credentials and password breaches due in part to people using the same password over and over. By eliminating the need for passwords and replacing them with a high-assurance authentication mechanism, you are in effect eliminating your company’s exposure – or attack surface – to the number one cause of cyberattacks and data breaches.
Productivity
A passwordless solution is an SSO method that allows users to verify themselves biometrically rather than by entering a password in order to gain access to all tools used by the company. Whether it’s a legacy application that lives on prem or a newer system in the cloud, passwordless authentication means instant and easy access to every tool that an employee might use during the workday. Especially now, when more and more employees are working remotely, it is critical to have easy (and secure) access from anywhere at any time. No more waiting for Bob from IT to be available to reset a password, and Bob from IT no longer has to spend hours out of his day responding to password reset requests. Everyone can be more productive – a win-win all around.
Compliance
With regulations and compliance standards such as SOC2 and PCI DSS constantly becoming stricter, companies are faced with the challenge of requiring employees to comply with (and remember) ever more complex password policies. Passwordless authentication ensures strict regulatory compliance without every employee needing to remember multiple passwords, each with its own unique set of rules.
It’s Time to Go Passwordless
According to Gartner, by 2022, 60% of large enterprises and 90% of midsize enterprises will implement passwordless methods in up to 50% of use cases. There’s no reason to wait until 2022 when you could start now and watch your productivity soar and your costs plummet, all while providing a much more secure environment.






