The largest Distributed Denial of Service (DDoS) attack ever seen hit the internet in March this year. It was aimed at CloudFlare network. 120 Gbps hit the edge of CloudFlare network, and in turn the upstream providers were hit by a massive 300 Gbps DDoS at the peak of the attack, according to eSecurity Planet. The usual ceiling of the attacks is 100 Gbps. Actually, most DDoS attacks are less than 100 Mbps in size. But the consequences remain the same. Extended downtime. Customer complaints. Revenue loss and mitigation costs. Erosion of brand value.
Source: http://www.akamai.com/stateoftheinternet/
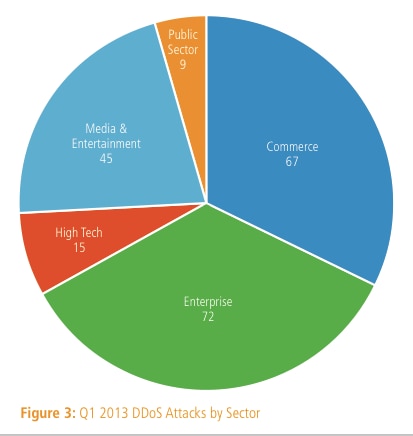
According to Akamai analysis of attacks reported by customers, across the full year 2012, 768 attacks were reported, and the number seems to be on the rise in 2013. Also, enterprise clients received a substantially greater percentage of attacks in the first quarter of 2013, accounting for 35% of all attacks (72 total), up 14% quarter over quarter (see Image 1/Figure 3 from the State of the Internet report).
Book a demo today to see GlobalDots is action.
Optimize cloud costs, control spend, and automate for deeper insights and efficiency.

According to Arbor Networks live data feed based on ATLAS data, and the active threat analysis, 2934 DDoS attacks per day are noticed worldwide, peak attack measured is at 253 Gbps and over a thousand botnets are detected. “Targeted attacks continue with great speed and require a resourceful defense combined with vigilance in order to block and detect such campaigns as quickly as possible,” they explain in the threat briefings, summarizing the most significant security events that have taken place over the past 24 hours. DDoS continues to be a global threat, with a clear increase in attack size, speed and complexity.
Summary of Key Findings from Arbor Networks Analysis
Escalation in the size, frequency and complexity of attacks is visible from ATLAS live data feed for the first quarter in 2013.
- average Bits Per Second (BPS) attack size is up 43% so far this year, 46.5% of attacks are now over 1Gbps, which is a jump of 13.5% from 2012
- proportion of attacks in the 2-10 Gbps range more than doubles, from 14.78% to 29.8%
- proportion of attacks over 10 Gbps increased 41.6%
- in the first half of 2013 we have seen more than double the total number of attacks over 20Gbps we saw in the whole of 2012
- attack durations are trending shorter, 86% now last less than one hour, Packets Per Second (PPS) attacks sizes also seem to be trending downward
Nature of DDoS attacks
Distributed denial-of-service (DDoS) attack means that the attacker/hacker is choosing one computer system as a master system to control sometimes as many as hundreds of thousands other computer systems, known as zombies or bots. They all work with a uniform goal of flooding the targeted host with as many communication packets as possible to stop the website from working. The attacks do not only affect businesses such as Amazon or Yahoo!, governmental bodies, and banking institutions, but also individuals, trading companies, file sharers and end-customers.
DDoS attacks tend to repeat themselves: For victims (sites) that were affected by the attacks in the past year, the aggressors would return at a later date to have a greater, longer lasting impact on the target.
Continual growth of the number of attacks: The number of DDoS attacks Akamai encounters shows every indication of continuing to grow, with nearly 5% more attacks being reported in the first quarter of 2013 as compared to the fourth quarter of 2012.
DDoS attacks are difficult to determine: Botnets are necessary to create the attacks and the command and control (C&C) infrastructures of these botnets are designed to protect their owners.
Tools for DDoS attacks are becoming more available to masses: Some major tools used in common DDoS attacks have such names as Tribe Flood Network (TFN), Trin00, Stacheldraht, and Trinity, and more are becoming available and downloadable on the internet.
DDoS attacks (even the smallest ones) inflict a grave toll on revenues: More companies in 2012 (74% vs. 65% in 2011) said a DDoS outage would cost them up to $10K per hour, potentially almost a quarter of a million dollars a day. 26% reported revenue risks at $50-100K per hour, according to Neustar.
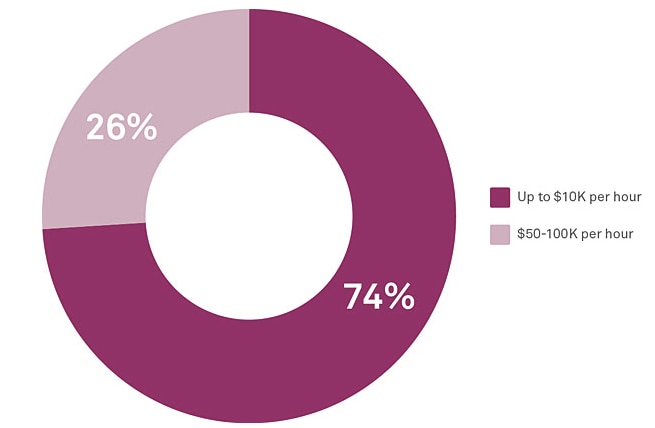
DDoS attacks inflict a grave toll on revenues, up to $50-100K per hour
Source: http://www.neustar.biz/enterprise/resources/ddos-protection/2012-ddos-attacks-report
DDoS attacks can last long: One third of the attacks in 2012 lasted more than 24 hours, some stretched for several days or longer, the longest attacks, increased from 10% to 13% in 2012, according to Neustar. 20% of all attacks lasted between 3 and 7 days. According to the latest report by Arbor, however, the attack durations are trending shorter, 86% last less than one hour
Single method of prevention is not enough to stop the attacks: A successful mitigation of DDoS attacks involves several defense strategies such as system updates, CDN hosting, disabling IP broadcast, IP address filtering, anomaly checks and more. The packets are never coming from a single source, and they can not be avoided by blocking a single IP address.
Read more:
- http://www.networkworld.com/news/2013/073013-ddos-attacks-arbor-272319.html
- http://www.arbornetworks.com/research/infrastructure-security-report
- http://www.akamai.com/stateoftheinternet/
- http://gigaom.com/2013/03/27/what-you-need-to-know-about-the-worlds-biggest-ddos-attack/
If you are under DDoS attack or just want to improve your security and prevent DDoS attacks, GlobalDots can help you mitigate the risks. Get in touch today and our team of specialists will help you keep your website and business secured.







