Simply put, an IP is an address that direct an Internet data stream where to go – it’s the core of internet browsing. It is often said, “the Internet is running out of phone numbers,” as a way to express that the Internet is running out of IPv4 addresses, to those who are unfamiliar with Internet technologies.
Just like phone numbers, IPv4 addresses are assigned hierarchically and have inherent inefficiency. Since the world Internet population is constantly growing and will continue to do so due to the extreme rise of Internet-connected devices, it seems that ARIN (American Registry for Internet Numbers) has finally ran out of IPv4 addresses. No need to worry though, the Internet will work just fine, but all organizations must now accelerate their efforts to deploy IPv6. In this blog post, we’ll try to explain the following turn of events, the role of ARIN, basics of IPv6 and the difference in security between IPv4 and IPv6.
Book a demo today to see GlobalDots is action.
Optimize cloud costs, control spend, and automate for deeper insights and efficiency.

What’s ARIN’s stake at IPv4?
The Internet Assigned Numbers Authority (IANA) delegates authority for Internet resources to the five RIRs that cover the world. ARIN has been managing the assignment of IPv4 and IPv6 addresses and Autonomous System (AS) numbers since the 1980’s. IPv6, the successor technology to IPv4 which was designed to address this problem and it currently supports approximately 3.4×10^38 network addresses. When the supply of IPv4 address space drops to 0.00000, then there will be no more addresses to allocate. If IPv4 addresses become available, then the policies in the NRPM will dictate that they are given out based on the Waiting List for Unmet Requests method. Until the IPv6 network is complete, there will still be a need for 50-70 million IPv4s. The question is: where are they gonna get them form? The well is dry.
When the internet was developed, the engineers and programmers that put it together had no idea that 4.3 billion IP addresses would ever be used. Everybody was aware of the potential, but nobody guessed how big the Internet is going to get. As the Internet began to grow, techniques like Classless Interdomain Routing (CIDR) and Network Address Translation (NAT) were used to extended life-support for IPv4 for almost two decades. Now ISPs are looking at using Carrier Grade NAT (CGN)/Large Scale NAT (LSN) to further prolong the use of IPv4.
So, what’s IPv6 like?
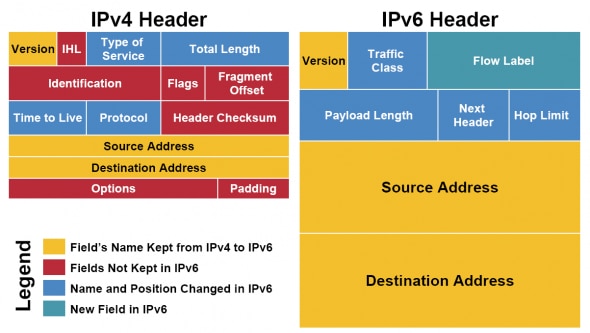
Like we’ve said, IPv6 supports 3.4×10^38 addresses, which is thought to be enough to give every single human being alive his or her own permanently allocated pool of unique IP addresses. The massive adoption of IPv6 means that more and more devices will be able to take advantage of the net. It also features mandatory security measures that should keep data in transit hidden, while each packet’s header information is simplified for more efficient processing by routers on the internet – thereby providing the internet in general with a much needed performance boost. Internet is far from safe and DDoS and other security threats have been on the rise for a couple of years.
The biggest difference between IPv4 and IPv6 is seen when you compare address formats. IPv4 uses four 8-bit sections called ‘octets’ and a similar netmask to carry details on the size of the subnet, the subnet number and the host number.
Tunnelling in Network adaptors using IPv6 have more than one IP address. For convenience, they have what’s called a ‘link-local’ address. This is an address that is only valid on the local subnet and always has the prefix ‘fe80::’ followed by the trailing four words that make up the host number.
Security – IPv6 vs IPv4?
Security is the cornerstone of IPv6’s design. In order for the hacker to sabotage a website, he has to identify running hosts on a subnet, but that task becomes more complicated because of the size of each subnet. Rather than simply pinging each possible host at once and causing a traffic storm that will alert any detection mechanisms to their presence, hackers will ping an initial address, wait a while, ping another random address, wait a while, and so on.
What’s so brilliant about IPv6 is that it’s impossible to check every possible IPv6 address within a reasonable time. Scanning addresses for hosts at a rate of one million per second results in a scan time of about 500,000 years. Good luck with that, hackers. Also, IPv6 implements IPSec as a standard, which means that traffic (including passwords, card details and the rest) should be safe from sneaky eavesdroppers. Unfortunately, viruses and worms that progress through email and other infected executables will remain the same under IPv6.
IPv4 uses a special address called a broadcast address. By spoofing the source address, a hacker can run a ‘broadcast amplification’ denial-of-service attack where the acknowledgements bombard his target. IPv6 doesn’t use broadcast addresses, meaning that this simple form of attack should become a thing of the past. One problem remains – the lack of understanding of IPv6 and the assumption that the new protocol is secure will surely lead to new kinds of attacks.
What’s next for the Internet?
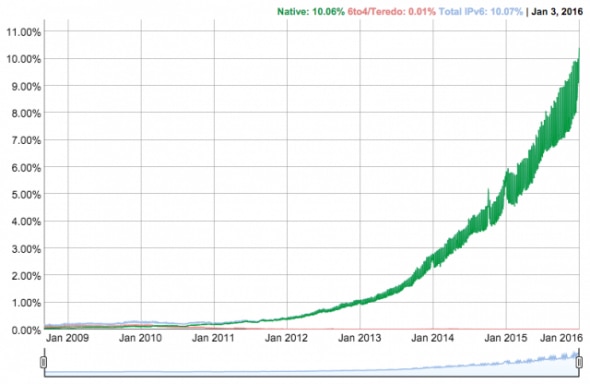
Google revealed that 10.09 percent of all traffic to its websites was made of IPv6 connections as of January 2 2016, nearly double that from the same time last year when the number was 5.47 percent. In terms of the number of IPv6 connections made per country, Belgium is currently leading the way with 44.32 percent, followed by Switzerland with 30.89 percent and the US with 25.63 percent.
Internet Service Providers should already be well on their way through their IPv6 deployments. If you’re running an online business, you can’t ignore IPv6 anymore – your organization should be planning for future years of legacy IPv4-Internet connectivity and should be actively moving toward full deployment of IPv6. Despite all of the improvements, the Internet still won’t be a safe place once IPv6 has been fully adopted, but still, it’s the next step of the Internet and online businesses would do well to embrace the trends ahead.






