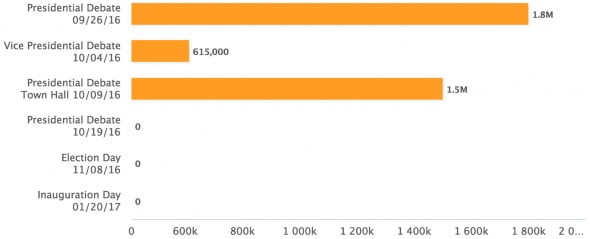
Numbers from this year’s Presidential debates
We already mentioned some very interesting statistics from Fastly in our last week’s news, but here’s some more debate numbers! Akamai made a page where all statistics from all major debate events are carefully depicted. Looking through this page, you will have a clear picture of just how much viewers are engaged in the elections by seeing the max peak traffic, audience size and average bitrate.
Read more: Akamai
Book a demo today to see GlobalDots is action.
Optimize cloud costs, control spend, and automate for deeper insights and efficiency.

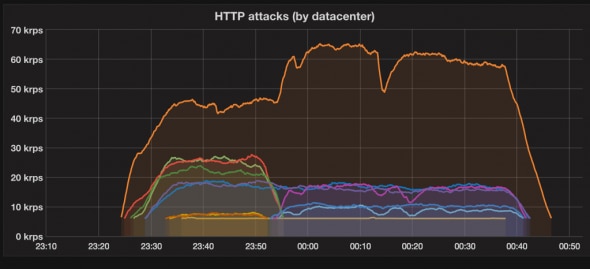
IoT DDoS attacks analysis by Cloudflare
Cloudflare endured some attacks in the near past that came from devices that had port 23 (telnet) open or closed, never filtered. Most of the hosts were Vietnamese networks that looked like connected CCTV cameras. Multiple had open port 80 with presenting “NETSurveillance WEB” page. These were all hints that the attacks were coming from an IoT (Internet-of-Things) category of devices. Cloudflare team measured these attacks by the number of requests and bandwidth. They also managed to approximately learn from where the attacks were coming from.
Read more: Cloudflare Blog
CDNetworks launches Cloud Image Optimization to improve brands’ web performance
Brands’ websites with high quality product images are now able to deliver a fast consumer experience across any device with new CDNetworks Cloud Image Optimization technology.
DNetworks Cloud Image Optimization allows brands to automatically optimise image performance and ensure a fast user experience, whether accessed on a desktop, tablet, or smartphone. Tests using a third party performance monitoring tool show that CDNetworks’ Cloud Image Optimization accelerates download speeds by 50-80% on desktops and mobile.
Read more: CDNetworks
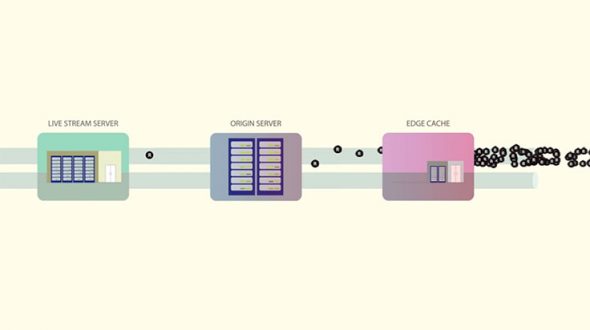
Facebook’s internal CDN for live videos
Live for Facebook Mentions is a feature that enables Facebook users to stream live video, and for this, they’ve rolled out their internal CDN (Content Delivery Network). This move brought with it a host of vexing logistical issues which needed to be solved. Problems like traffic spikes (thundering herd problem) and load balancing needed to be addressed for millions of users trying to access different live streams. Now, rather than letting clients connect directly to the live stream server, Facebook set up a globally distributed network of global edge caches. They’ve also enabled RTMP playback to shorten the latency in live broadcasts to just a few seconds.
Read more: Bizety, Facebook Code
More about IoT
More about IoT, this time the topic is: devices. Akamai published a small article which features a list of most used devices for IoT attacks. If you own any of these devices you can also protect yourself & your devices from being used in a distributed attacks by using their End-User Guidance that is also contained in the article. Here’s the list:
- CCTV, NVR, DVR devices (video surveillance)
- Satellite antenna equipment
- Networking devices (e.g. Routers, Hotspots, WiMax, Cable and ADSL modems, etc.)
- Internet connected NAS devices (Network Attached Storage)
Read more: Akamai Blog






