The internet slowed to a crawl due to a BGP route leak
On November 6th for a little more than 90 minutes internet service for millions of users in the U.S. and around the world slowed to a crawl. This time it wasn’t a botnet threat but yet another BGP route leak. A BGP route leak is a router misconfiguration directing internet traffic from its intended path to somewhere else which is definetly a problem, especially when it happens to one of the largest telecommunications network in the world.

Read the full report: Dyn Blog
Book a demo today to see GlobalDots is action.
Optimize cloud costs, control spend, and automate for deeper insights and efficiency.

DDoS-for-Hire service launches mobile app
Ragebooter, a service paying customers can use to launch powerful DDoS (Distributed Denial of Service) attacks capable of knocking individials and entire websites offline can now be downloaded on the Google Play Store. The entire story behind this app is a bit more complicated. The creator of Ragebooter is Justin D. Poland who, after prison, still decided to continue running it even though it directly breaks his parole.
In October, the FBI released an advisory warning that the use of booter services otherwise called “stressers” is punishable and may result in arrest and criminal prosecution.

Read more: KrebsonSecurity
Amazon’s C5 instances are now available
Amazon added C5 instances to EC2 which are available in the company’s US East, US West, and EU regions. C5 Instances which are available in five sizes, each offering a different bandwidth for high-powered applications, enable businesses to run compute-intensive applications such as batch processing, distributed analytics, ad serving, high-intensity multiplayer gaming and video encoding.
“Over the years we have been working non-stop to provide our customers with the best possible networking, storage, and compute performance, with a long-term focus on offloading many types of work to dedicated hardware designed and built by AWS”
– Jeff Barr (AWS Chief Evangelist)

Read more: CloudPro
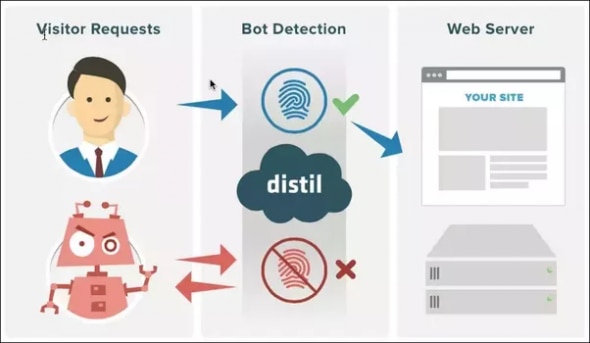
Distil launches new JavaScript deployment option
Distil announced additional enhancements to its Bot Defense Platform which makes their new JavaScript deployment option available to its customers. The new method enables companies to block bots in multiple settings, whether in the data center, via proprietary infrastructure, Secure CDN, on AWS, or through JavaScript integration. By using the deployment, Distil customers can integrate the product into their own code without making any infrastructure changes.
Read more: Bizety
The Equation Group is back
For the last two decades, according to Kaspersky Lab, an incredibly sophisticated threat actor named the “Equation Group” has been active. It caught their eye mainly because of its advanced obfuscation techniques and penchant for encryption algorithms. They’ve documented 500 infections by the Equation Group in 42 countries, which they’re sure is just a tiny percentage of the total because of its built in self-destruct mechanism. Kaspersky Lab named this attack the most sophisticated attack in the world, comparing it to the Death Star in the APT universe. They even went so far and started claiming this is the handwork of NASA.
Read the full story: Bizety






