Banks in the UK & Russia are under attack & the TrickBot Trojan
Starting with the Tesco bank in the UK, where the entire savings accounts of 20,000 customers have been wiped out by the attackers, you can already see where this news update is going. They’re still investigating the incident and have promised that appropriate compensations will be made to the affected customers. Another attack worth noting has been performed on Russian banks. This attack is a bit more straightforward as it is a DDoS attack from IoT devices (sounds familiar?) that compromised five major Russian banks’ online systems and websites. In other news the TrickBot Trojan is reported to now be fully operational which means people visiting their banks’ website can be easily affected by a trojan more sophisticated than ever.

More about the Tesco Bank attack: Hacking Threat
DDoS attack against Russian banks: Hacking Threat
TrickBot Trojan: Hacking Threat
Book a demo today to see GlobalDots is action.
Optimize cloud costs, control spend, and automate for deeper insights and efficiency.

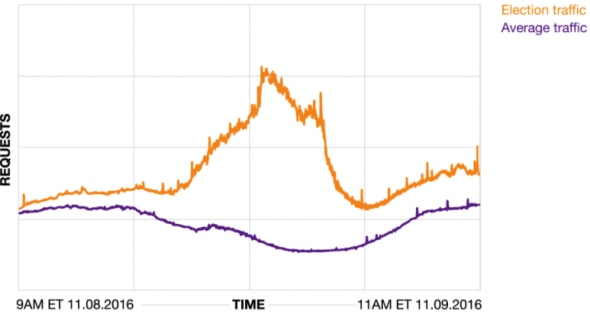
Real time insights from the US elections
Fastly made an interactive informational page that illustrates traffic spikes and analysis of all the major election events including the election day. Given they power tens of thousands of websites, they have an unique position to gather key insights into how users react online to different events. Akamai also joined in with their analysis page and conveniently joked about how the Canadian Immigration Website was also offline after the elections.
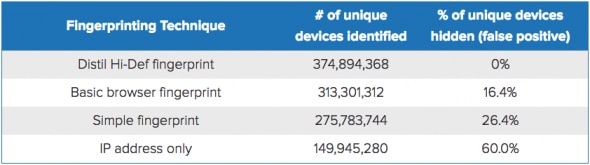
Distil Networks introduced Hi-Def Fingerprinting
Hi-Def fingerprinting is an augmented device fingerprinting method that identifies unique devices more accurately than standard techniques. They’ve compared the successfulness of their new technology against older fingerprinting technologies and the results are apparent as seen in the table below.
The Linkedin phishing scam
Linkedin Premium users were affected by a new scam that solicits users’ credit card information, driver’s licences, and passports. Linkedin paying users were targeted with a phishing email that contained a number of sophisticated details designed to trick users. Here’s the email:
Hi [name],
Thank you for being our valued customer. Your account has been selected by our verification office as a precautionary measure to defend you. Upload a viewable, scanned copy of the payment method account holder’s government-issued photo identification, such as a driver’s license or passport.
Upon receipt and verification, we will notate your account that the necessary documentation to substantiate your account has been received. We thank you in advance for your cooperation and apologize for any inconvenience this may cause.
The image must be a color scan that shows your photo and required data clearly.
This link will expire in 24 hours, so be sure to use it right away.
Thank you for using LinkedIn!
The LinkedIn Team
Read more: Hacking Threat
China introduces more stricter cybersecurity laws
After June 2017 a law in China will be introduced that will put new strict regulations on technology companies operating in the country. The law was created amidst the growing cyber threats such as hacking and terrorism and it comes with data localization, surveillence, and real-name requirements. This regulation means that from that point, all instant messaging services and other internet companies will require from their users to register with their real names and personal information, all “prohibited” content will be censored and the list goes on. China already has one of the largest government-enacted restrictions on the internet, known to many outside of the country as the Great Firewall and this does now help their case as human rights advocacy groups are being increasingly alarmed.
Read more: Hacking Threat






