They’re not interchangeable. A vulnerability assessment identifies known flaws at scale. A penetration test mimics an actual attacker probing for impact.
Yet many teams treat them the same. They substitute one for the other, check a compliance box, and move on as if they’re covered.
Book a demo today to see GlobalDots is action.
Optimize cloud costs, control spend, and automate for deeper insights and efficiency.

They’re not. And that gap shows up later in real-world breaches.
This article removes any confusion. You’ll get a grounded comparison of both methods, when to use each, and why a hybrid approach often delivers the most complete view of your exposure.
What Is a Vulnerability Assessment?
A vulnerability assessment is a structured, automated scan of your systems to identify known security weaknesses. It’s broad, repeatable, and optimized for scale. Not stealth (this is important later).
Most organizations use vulnerability assessments to:
- Continuously monitor for outdated software, missing patches, and misconfigurations
- Establish a baseline security posture
- Meet compliance requirements with minimal disruption
Scanners rely on databases of known vulnerabilities (like CVEs) and run checks against your network, OS, applications, and APIs. Tools like Qualys, Nessus, or OpenVAS are common in this space.
Typical output includes:
- Lists of discovered vulnerabilities, categorized by severity
- System configurations out of policy
- Patch recommendations or upgrade paths
They’re fast and low effort ,but not exhaustive. Vulnerability assessments rarely validate exploitability. They don’t chain issues together or test business logic. You’ll get coverage, but not always context.
What Is Penetration Testing?
Penetration testing is a simulated cyberattack performed by security experts to evaluate how well your systems resist real-world intrusions. Unlike automated scans, pen tests are human-driven and goal-oriented.
They mimic threat actor tactics to answer a different question: if someone wanted in, could they get in, and what could they do next?
Pen tests come in several formats:
- Black box: No internal knowledge. Testers act as external attackers.
- White box: Full visibility into the environment, including source code and credentials.
- Gray box: Limited context, often mimicking insider threats or compromised credentials.
Penetration testing focuses on:
- Exploiting weaknesses (not just detecting them)
- Mapping attack paths and chaining vulnerabilities
- Bypassing security controls through misconfigurations, logic flaws, or weak authorization
It’s labor-intensive and time-boxed, often run quarterly or annually. Output includes an executive summary, technical details, and remediation guidance. For many companies, it’s also required for compliance (PCI DSS, ISO 27001, SOC 2).
Pen testing goes deeper, but not wider. It doesn’t scale across every system or update. That’s where it complements vulnerability assessments.
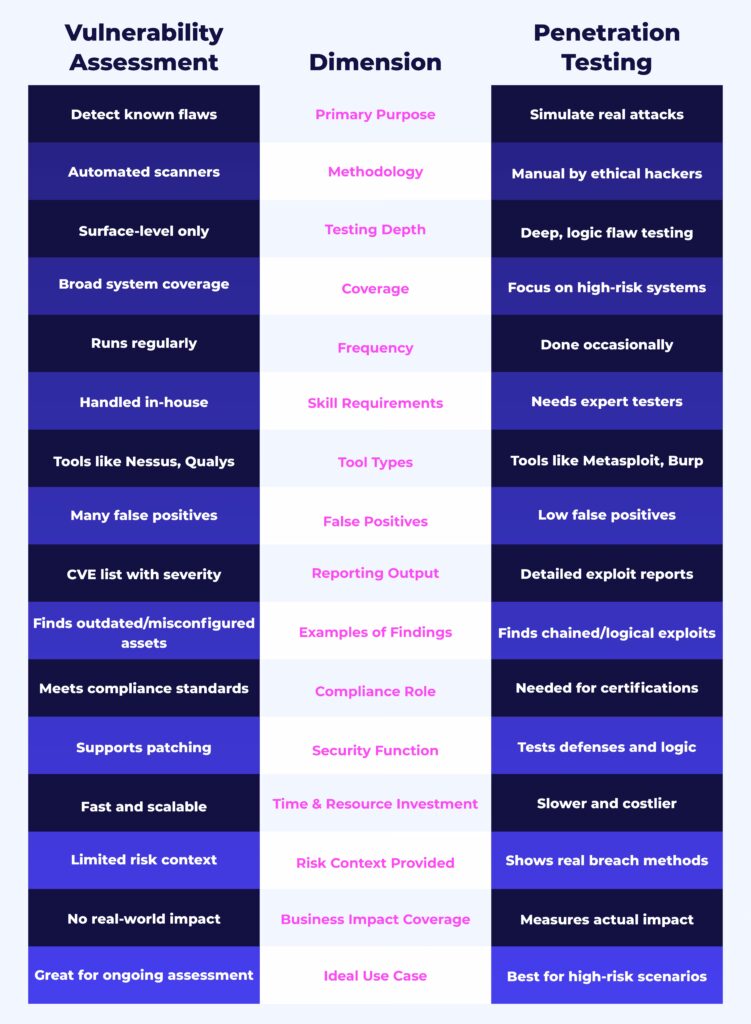
Vulnerability Assessment vs. Penetration Testing: Key Differences
These two methods serve different purposes. Here are the key differences:
Before we proceed here, let’s clear out some common misconceptions around vulnerability assessment and penetration testing:
- A pen test is not just a fancier vulnerability scan. It’s a targeted attack simulation.
- A vulnerability scan doesn’t confirm exploitability; it flags potential issues.
- You don’t need to choose one over the other. They address different layers of the security stack.
Together, they close different gaps. One keeps your baseline clean while the other tells you if that baseline holds under pressure.
When to Use Each
Choosing between vulnerability assessments and penetration testing depends on your goals, risk profile, and maturity stage. Most organizations need both, but not with the same cadence, scope, or purpose.
First, define the scope:
Before running any test, clearly define the scope. Not every asset, system, or environment will be included, and that’s intentional. Scope definition aligns the test with business priorities, compliance requirements, and resource availability.
For vulnerability assessments, scope determines which networks, endpoints, cloud assets, containers, or apps are regularly scanned. You might exclude production environments or third-party systems depending on data sensitivity or contract boundaries.
For penetration tests, scope is even more critical. Tests are intrusive by design. You’ll need to document:
- Which systems are in bounds (e.g., public-facing web apps, specific cloud resources)
- Which ones are out of bounds (e.g., core production databases, regulated systems)
- Whether the test is black-box, white-box, or grey-box
- Any time or operational constraints (e.g., “no testing during business hours”)
Scope ensures tests are safe, targeted, and legally authorized. And it helps prevent disruption to critical operations.
With scope clearly defined, you can choose the right type of test for the job.
Use a vulnerability assessment when:
- You want frequent visibility into known weaknesses.
- You need to maintain compliance with continuous scanning (PCI DSS, HIPAA).
- You’re building or updating a vulnerability management program.
- You’re onboarding new infrastructure or migrating to the cloud.
- You want to feed patching priorities into your SecOps workflow.
Use a penetration test when:
- You need to simulate real-world attacker behavior to test your defenses.
- You’re preparing for or maintaining compliance (e.g., PCI DSS requires annual pen tests).
- You want to validate whether existing controls actually stop attacks.
- You’ve had a breach or suspect business logic abuse.
- You’re preparing to go live with a critical application or major change.
Frequency guidelines:
- Vulnerability assessments: Weekly to monthly or integrated into CI/CD where possible.
- Penetration testing: At least once a year, plus after major architectural or application changes.
Vulnerability scans give you breadth. Pen tests give you depth. The right schedule combines both, depending on asset risk, exposure, and industry standards.
This Is Why You Likely Need Both
Too many security teams treat vulnerability scans as checkboxes and pen tests as annual rituals. Neither is enough on its own. Cyberattacks aren’t waiting for quarterly audits. If your security testing is lagging, you’ve already lost ground.
Here’s why we recommend a hybrid strategy:
- Coverage vs. context: Scans catch wide swaths of known issues fast. Pen tests reveal how attackers actually get in. You need both to understand exposure, not just vulnerability.
- Modern threats demand realism: Automated scanners won’t catch chained exploits or business logic flaws. Attackers will. Simulating their methods closes that gap.
- Compliance favors layered testing: Frameworks like PCI DSS, ISO 27001, and SOC 2 increasingly expect both routine scans and validated attack simulation.
- DevSecOps needs velocity and insight: Automated scans keep pace with rapid deployment. Pen tests expose what slipped through.
At GlobalDots, we help teams design the right testing cadence, pick the best-fit tools, and close the loop with prioritized remediation. Whether you need ongoing assessments, red team validation, or both, we help security shift from reactive to ready.
Key Takeaway: Scanning Alone Isn’t Security
Security testing isn’t about checking boxes. It’s about knowing what attackers can see, what they can exploit, and how quickly you can close those doors.
Vulnerability assessments and penetration tests serve different roles. One gives you constant visibility into weak spots. The other shows you how those weak spots can be used against you. Together, they build a layered, informed defense strategy.
If you’re still choosing between the two, you’re asking the wrong question. Most organizations need both, but in the right cadence, using the right tools, and mapped to their real risks.
GlobalDots helps security teams get that balance right. We’ll assess your environment, define a fit-for-purpose testing approach, and help you prioritize what matters most. Whether you need automated assessments, ethical hacking, or help operationalizing remediation, we’re ready.
Talk to our security team
Let’s make your exposure manageable






