The world of digital publishers is being plagued with bots. Data breach is a main concern for anyone running an e-commerce business. The research shows that only 40% of digital publishers can distinguish between good bots, bad bots and human traffic and over half of those have their data stolen by nefarious online actors, also known as cyber criminals. Not only criminals, but also competitors threat leveraging bad bots.
We have chosen a few methods that can help you measure and mitigate this problem, as well as define those problems, whether you deploy via physical or virtual appliance or a cloud CDN. Actionable threat intelligence is the key to effective cyber threat detection and response. In these short overview, we will go through the types of digital ad fraud, the scale of these frauds in terms of money loss for retailers. We will also inspect how botnets function, how bad bots impact everything from brand reputation, competitiveness, revenue and cost perspectives and what are the precaution measures that you can make yourself or leave it to a third party as we are entering the bot era where more retailers are to trust companies that build smart bots, and their expertise in machine learning.
Book a demo today to see GlobalDots is action.
Optimize cloud costs, control spend, and automate for deeper insights and efficiency.


Types of digital ad fraud
Click fraud is a type of fraud that occurs on the Internet in pay-per-click (PPC) online advertising when a person, automated script or computer program imitates a legitimate user of a web browser clicking on an ad, for the purpose of generating a charge per click without having actual interest in the target of the ad’s link.
Impression fraud is an invalid traffic generation that aims to inflate advertising impressions on websites. For this, Pay Per View (PPV) networks need to be identified, that are comprised of legitimate websites that use JavaScript provided by PPV network service providers to render unwanted web pages “underneath” requested content on a real user’s browser so that additional advertising impressions are registered.
Skewed analytic data signifies a lack of visibility into some type of activity of your users that could be skewing your data, leaving you unaware of an entire segment of customers that purchase, or prefer to purchase, via a phone call, for example.
The scale of digital ad fraud
If 56 billion dollars is estimated to be in circulation in the digital ad world, than 1 in 3 of these dollars is wasted on bots. We offer two examples, that of Ashley Madison Breach and Bob Carr and Heartland Payment System breach. In July 2015, a group calling itself “The Impact Team” stole the user data of Ashley Madison, a commercial website billed as enabling extramarital affairs. The group copied personal information about the site’s user base and leaked 32 million log-in credentials into the wild. In the case of Bob Carr, way back in 2008, after Heartland’s network was breached, this lead to the compromise of some 130 million credit and debit cards.
Heartland’s breach cost card issuing banks and credit unions about $500 million. If the same type of processor breach were to occur today, Carr said the cost to banks and credit unions would likely be billions of dollars, and there’s no way Heartland, or any other processor or retailer, could afford to pay issuers the full amount to cover that cost. Today, approximately 1.4% of online revenue is lost to fraud. In 2015, the average total cost of a data breach was estimated at $3.79 million, a 23% increase from 2013.
Robot and network

In order to protect your commerce from losing money to frauds, it is useful to understand how bots are functioning. They are actually connected computers communicating to other internet-connected computers in what is known as botnet. They are not always malicious, as in their essence they were built for communication. But many times they are used for coordinating DDoS attacks or spam campaigns. A compromised device, known as “bot” is created when a computer is penetrated by software from malware distribution. It could also be a “spider” that hacks into the computer. The controller of a botnet is able to direct the activities of compromised computers through communication channels formed by standards-based network protocols such as IRC and HTTP. A “bot herder” or “bot master” can then control the group remotely, usually through IRC or Domains, and often for criminal purposes.
Blocking IP addresses in order to prevent these attacks does not work any more as a protection but you need a purpose built solution that will use machine learning to refine these profiles in real time, learn through patterns, and then ad malicious behaviors to bots/violators database.
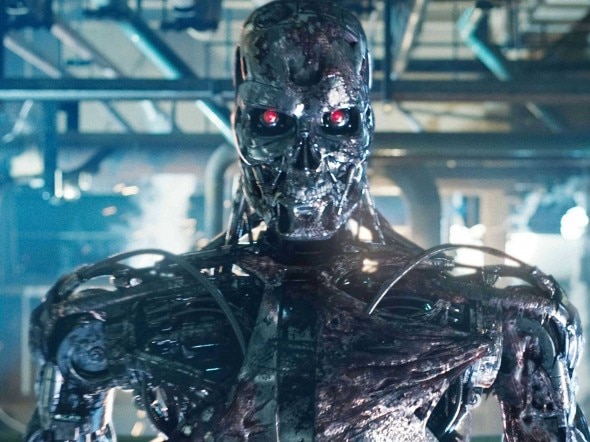
From the image (Wiki) it is visible in which ways botnets can work. They can send viruses or worms to a computer whose payload is then going to become a “bot”. Or, they can send Trojans, through e-mail, for example. The bot will then log into a C&C server, that is, command and control server that belongs to a bot herder. Spammer will then purchase services of the botnet from the operator by providing spam messages. This endangers overall security of e-commerce website, loyal consumers and your brands, your SEO and costs money.
Bad bots impact online retailers from competitive, revenue and cost perspectives
Malicious bots create significant challenges for both organisations and end-users by creating high false positive rates and by generating risk scores. Advertisers, publishers and end-users need to be able to distinguish between legitimate and malicious activities in real time. Authentication methods such as out-of-band, one-time passwords and security questions can all be bypassed easily and with minimal effort by violators. While more sophisticated authentication methods have been developed, the customer experience has been compromised.
Botnets can be exploited for various purposes, including denial-of-service attacks, creation or misuse of SMTP mail relays for spam, click fraud, mining bitcoins, spamdexing, and the theft of application serial numbers, login IDs, and financial information such as credit card numbers. This instantly impacts brands, damaging their SEO and stealing content, causing slowdowns and downtime. Bots are scraping, spamming and proning for vulnerabilities. Bot attacks instantly endanger your:
CTR: click through ratio rate &
Importance of prevention of bot attacks and brand trust
Digital publishers that care about their brand trust need to find solutions to prevent ad serving resources and revenue to be wasted on bots. Doing an e-commerce business is no longer possible without some kind of a digital transaction. For the transaction purposes, ad-buyers and ad-sellers are willing to pay more for human traffic, or more correctly, this is 37% of ad-buyers, the research shows.
Of these, 10% are willing to pay even 50 to 100% more. In opposition, 59% of ad buyers are willing to pay more for non-human traffic. Buyers today are unable to ensure they reach humans. 50% of ad-buyers and ad-sellers report they are unable to measure non-human traffic. Digital ad fraud is of a top concern for digital publishers. In order to protect brand reputation amongst ad networks, you need to:
ensure that your servers load at the optimal speed, without downtimes or slowdowns since most users will abandon page if it loads in under 4 seconds (take into account the rise of mobile users, including tablets)
you must be able to detect bad bots
eliminate false positives
prevent from stealing user data
create safe and reliable environment
since traffic from all sources arrives for identification, you must be able to filter out non-human and fraudulent traffic by using validation tools to audit ad-inventory
measure viewability
There are multiple mediums through which Web traffic consumes content and ads; a growing number of ads are served on mobile devices, within online videos, and within emails. These means: display ads, e-mail ads, mobile ads, video ads. Each of these channels has a number of unique characteristics that impacts the value of the ads to advertisers, and therefore the expected revenue to the publishers.
Precaution measures
Threats of automated website interaction lead to grand theft of customer property. In order to prevent this you can take some precaution measures as presented below, or leave this to a third party, as also suggested. You should:
install proper network security
double your authentication system
prioritize data and define what requires the most stringent control
collect and analyze meaningful information about your cyber security
present findings to key stakeholders
know what assets are valuable to your business and to others
take proactive steps in anticipation of attack
hire a third party to supplement your information security
make your network less static
move data around, change your network design
always monitor for signs of alarm
The Bot era
With the rise of mobile device, “there are more than 1.5 million apps on iOS, and 1.6 million on Android. The apps have given rise to a host of new services: for hailing rides or for ordering takeout, for booking travel, or for messaging co-workers,” reports the Verge and continues: “In the desktop era, the glue that bound everything together was the search engine, routing us from Wikipedia to Orbitz to Priceline to Yelp. In the mobile era, that glue is the application programming interface — the API — a bit of software that allows apps to talk to each other. It’s an API that lets you upload a photo from your phone to Facebook, or order an Uber from the Google Maps app.”
All this gave rise to the bot era where large enterprise software companies are all going to invest in building smart bots that scrape content, and retailers will rely on these companies expertise in machine learning to help with security. But on a criminal part, a large scale account takeover is each day more possible because of bots. In a brute force attack, bot could be stealing usernames and passwords and create new accounts which are than used for various types of ad fraud, as already explained. Bot powered fake account registration could be used to create so called “synthetic” identities with which criminals evade detection and execute new account fraud at scale. It is important to remember that fake accounts run by bots hurt conversions, trick legitimate users and create fraudulent transactions which directly influences your revenue and brand reputation.






